All posts tagged "Cybersecurity"
-

Vulnerabilities
/ 2 months agoAdobe Reader Zero-Day Exploit Actively Steals Files, Threatens Full System Takeover
A Stealthy PDF Threat Emerges Security researchers are sounding the alarm about a highly sophisticated and currently unpatched vulnerability in Adobe...
-


Vulnerabilities
/ 2 months agoGitLab Issues Urgent Patch for Critical Flaws: DoS and Code Injection Risks Addressed
Critical Security Update Mandatory for Self-Managed GitLab Instances GitLab has sounded the alarm, releasing a substantial security update that patches a...
-


Vulnerabilities
/ 2 months agoCritical Palo Alto Networks Flaw Lets Attackers Bypass Authentication in Microsoft Teams Integration
A High Stakes Security Breakdown Palo Alto Networks has rushed out a critical security patch, and for good reason. A severe...
-


Vulnerabilities
/ 2 months agoCritical SonicWall SMA1000 Flaws Uncovered: SQL Injection and Privilege Escalation Threaten Secure Access
A Serious Blow to Secure Remote Access Gateways SonicWall has sounded a stark alarm for organizations relying on its secure remote...
-


Vulnerabilities
/ 2 months agoHow a Simple Code Leak Sparked a Sophisticated GitHub Malware Campaign
The High Stakes of a Packaging Error In the world of software development, a routine update is supposed to be a...
-


Vulnerabilities
/ 2 months agoCritical Windmill Platform Vulnerabilities Expose Systems to RCE, PoC Exploit Released
Severe Security Flaws Uncovered in Windmill Automation Platform Cybersecurity researchers have sounded the alarm on a series of critical vulnerabilities within...
-

Vulnerabilities
/ 2 months agoAI Uncovers 13-Year-Old Apache ActiveMQ Flaw, Highlighting New Era of Vulnerability Discovery
A Hidden Flaw Surfaces After More Than a Decade The security landscape is witnessing a paradigm shift, not just in the...
-


Vulnerabilities
/ 2 months agoThe Silent Listener: How Fiber Optic Cables Can Be Turned into Covert Microphones
A New Frontier in Acoustic Surveillance For decades, fiber optic cables have been the gold standard for secure, high-speed data transmission....
-

Cyber Attack
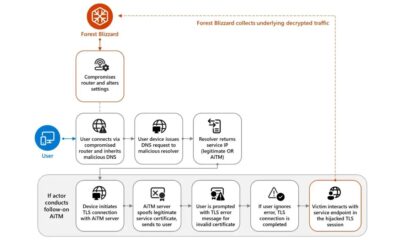
/ 2 months agoRussian State Hackers Hijack Home Routers in Global Espionage Campaign
The Unseen Gateway: How Home Routers Became a Spy’s Dream Imagine the digital front door to your home office, the humble...
-


Vulnerabilities
/ 2 months agoCritical Dgraph Vulnerability Exposes Databases to Unauthenticated Takeover
A Severe Oversight in Dgraph’s Security Layer A critical security vulnerability has been uncovered in the open-source Dgraph graph database, posing...