A Trusted App Becomes a Trojan Horse
In a stark reminder that security threats often exploit trust, not just code, a sophisticated attack campaign has weaponized the popular note-taking application Obsidian. The operation didn’t rely on a zero-day exploit or a complex software vulnerability. Instead, it cleverly manipulated the app’s legitimate plugin ecosystem and user-driven features to deliver malware across both Windows and macOS systems. This incident transforms a tool beloved by developers, writers, and knowledge workers into an unwitting launchpad for malicious activity, challenging conventional security assumptions.
The Social Engineering On-Ramp
The campaign began not with a malicious download, but with a convincing persona on LinkedIn. Posing as a venture capitalist, the attackers initiated contact with potential victims, eventually moving conversations to the encrypted messaging app Telegram. This shift to a less-monitored platform is a classic tactic, building a facade of legitimacy and confidential business discussion. The hook was an Obsidian vault, a collection of notes and configurations, which the attackers claimed contained valuable investment information or project details.
Once a target opened this shared vault, the attackers then persuaded them to enable “community plugin sync.” This feature, designed for convenience, allows plugin settings to synchronize automatically across devices. In this case, it became the delivery mechanism for a weaponized configuration. The attackers had pre-loaded the vault with a malicious setup for the legitimate “Shell Commands” plugin, a tool that lets users run custom scripts. By syncing, the victim unknowingly imported and activated this booby-trapped configuration on their own machine.
Dual-Platform Payloads and Evasion Tactics
The beauty, and danger, of this attack lay in its platform-aware design. The weaponized Shell Commands plugin triggered different infection chains depending on whether the victim was using Windows or macOS. This cross-platform capability significantly broadened the threat actor’s potential target pool, making the campaign more versatile and dangerous.
The Windows Infection Chain
On Windows systems, the plugin executed a multi-stage PowerShell script. This script acted as a loader, fetching encrypted malware, decrypting it in memory, and executing it without ever touching the disk, a technique known as fileless execution. The final payload, dubbed PHANTOMPULSE by Elastic Security researchers who discovered the campaign, is a fully-featured Remote Access Trojan (RAT).
PHANTOMPULSE is no simple info-stealer. It possesses a concerning array of capabilities, including process injection, screenshot capture, keylogging, privilege escalation, and even a self-uninstall function. Its use of AES-256-CBC encryption, dynamic API resolution, and reflective loading demonstrates a high degree of sophistication aimed squarely at evading traditional antivirus solutions that scan written files.
The macOS Infection Path
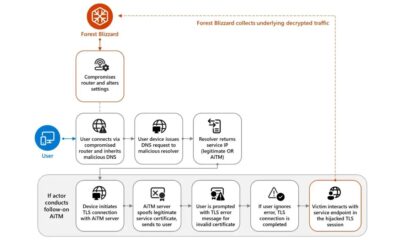
The macOS attack took a different route, leveraging native Apple scripting. The plugin launched a Base64-encoded command that executed an obfuscated AppleScript dropper. This script established persistence by creating a LaunchAgent, ensuring the malware would reactivate after a reboot. It then communicated with a command-and-control (C2) server through a layered process to fetch the next stage of the infection.
Perhaps the most ingenious part of the macOS chain was its resilience. If the primary C2 server was blocked or unavailable, the malware had a fallback mechanism: it could retrieve a backup domain from a dead drop resolver hosted on Telegram. This design makes simple domain blocking largely ineffective, as the malware can dynamically switch to a new communication channel, ensuring operational continuity for the attackers.
Why This Attack Bypasses Traditional Defenses
This campaign is a masterclass in living off the land and abusing trust. The attackers didn’t need to find a bug in Obsidian itself. They simply misused its intended, legitimate features. The Shell Commands plugin is designed to run user scripts; the sync feature is designed for convenience. Combined with effective social engineering, these features became potent weapons.
Furthermore, because Obsidian is a trusted, signed application, any malicious process it launches inherits that trust. This significantly weakens security models that rely on application allowlists or that view known-good software as inherently safe. From a system’s perspective, Obsidian was just doing its job, launching a child process as it often does for legitimate plugins. The malicious activity only became apparent after that point, often too late for prevention.
Detection and Mitigation Strategies
For security teams and vigilant users, several indicators can signal this type of compromise. Unusual child processes spawned by Obsidian, such as PowerShell, osascript (for AppleScript), curl, or other command-line utilities, should raise immediate red flags. Organizations should also monitor for new or modified files within the `.obsidian/plugins/` directory and unexpected changes to community plugin sync settings.
Network traffic provides another detection vector. Outbound connections to unfamiliar domains, especially those linked to blockchain resolution services or newly registered addresses, are strong indicators of C2 communication. The most practical mitigation, however, is policy-based. In managed enterprise environments, restricting the use of community plugins or requiring strict approval processes can shut down this attack vector entirely.
The Evolving Landscape of Software Trust
This incident forces a recalibration of how we perceive application security. It’s no longer sufficient to vet just the primary application; the entire extensibility ecosystem must be considered part of the attack surface. Plugins, themes, sync features, and shared workspaces all introduce new trust boundaries that can be manipulated. The line between a powerful, customizable tool and a security risk becomes blurrier with every feature added for user convenience.
Looking ahead, we can expect threat actors to continue targeting the connective tissue of our digital workflows. Applications that blend cloud sync, user collaboration, and extensible plugins are particularly attractive targets. The defense, therefore, must evolve beyond scanning for malicious files to understanding behavioral chains. Security tools will need to better model normal application behavior, recognizing when a trusted app like a note-taker starts behaving like a launchpad for script engines and network callbacks. In this new paradigm, the question isn’t just “is this file safe?” but “why is this trusted application asking to do that?”