A Coordinated Campaign Against Industrial Control Systems
In a stark warning issued on April 7, 2026, a coalition of U.S. federal agencies alerted the nation to an active and sophisticated cyber campaign. Iranian-affiliated advanced persistent threat (APT) actors are systematically exploiting internet-connected programmable logic controllers (PLCs), the digital brains behind physical industrial processes. This advisory, formally designated AA26-097A, directly links this disruptive activity to the operational ecosystem of the CyberAv3ngers persona, a group the U.S. government attributes to Iran’s Islamic Revolutionary Guard Corps Cyber-Electronic Command (IRGC-CEC).
From Hacktivist Persona to State-Sponsored Sabotage
CyberAv3ngers first appeared on the scene around 2020, initially masquerading as a hacktivist collective with a strong anti-Israel narrative. Over time, however, the facade has crumbled under the weight of evidence. Independent cybersecurity research and U.S. government sanctions have conclusively shown that the group’s funding, infrastructure, and advanced tooling are hallmarks of a state-directed program, not a loose band of activists. In 2024, the Treasury’s Office of Foreign Assets Control (OFAC) sanctioned six IRGC-CEC officials for orchestrating CyberAv3ngers operations, while the State Department placed a multi-million dollar bounty on the key operator known as “Mr. Soul.”
Subsequent intelligence leaks have further cemented this connection, revealing shared infrastructure and operational overlaps with other Iranian threat personas like Moses Staff. This paints a picture of a coordinated, state-run cyber ecosystem rather than isolated hacking teams. The group’s public claims, therefore, must be viewed with extreme skepticism; they are often part of a deliberate influence campaign designed to sow fear and distrust.
The Real-World Impact on Critical Infrastructure
The technical intrusions are far from mere propaganda. The joint advisory confirms that organizations across Government Services, Water and Wastewater Systems, and the Energy sector have already suffered tangible harm. Attackers have successfully caused PLC disruptions, manipulated data on Human-Machine Interface (HMI) and SCADA systems, and inflicted both operational and financial damage. Imagine a water treatment plant’s controls being tampered with remotely, or an energy substation’s sensors feeding false data to operators. The potential consequences extend far beyond a compromised website.
This shift from data theft to physical disruption marks a dangerous escalation in the cyber threat landscape. It demonstrates that adversaries are not just interested in stealing secrets but are actively probing for ways to cause real-world chaos and erode public confidence in essential services. The question is no longer if they can cause damage, but how much they are willing to risk.
The Theater of Cyber Disinformation
Parallel to its technical attacks, CyberAv3ngers runs a sophisticated propaganda machine. Analysts at firms like DomainTools have described their strategy as “engineering beliefs.” The group frequently recycles stolen screenshots and data, often from breaches conducted by allied groups, to fabricate or wildly exaggerate their claimed successes. Their goal is to create a media spectacle that amplifies fear, regardless of the actual technical impact on the ground.
A prime example was the group’s much-publicized October 2023 claim of breaching Israel’s Dorad power station. Later analysis revealed the “evidence” relied on reused imagery from an older Moses Staff leak. Yet, the theatrically packaged disinformation successfully shaped global media coverage and security discussions for days. This dual-pronged approach combining cyber-physical attacks with information operations makes them a particularly resilient and troublesome adversary.
Practical Defenses for Operators and Security Teams
So, what can organizations running industrial environments do? The guidance from advisory AA26-097A, supported by research from firms like Tenable, provides a clear roadmap. The first and most critical step is a simple one: disconnect PLCs and other operational technology (OT) controllers from direct internet exposure wherever physically possible. If remote access is absolutely necessary, it must be fortified with strong multi-factor authentication (MFA) and comprehensive logging, moving beyond vulnerable consumer-grade remote access tools.
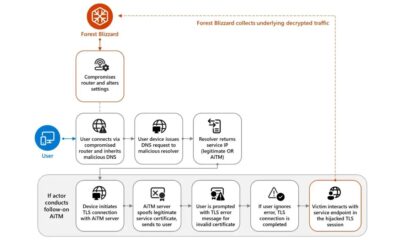
Network segmentation is non-negotiable. Engineering workstations and controllers must reside on networks strictly segregated from general business IT systems. This creates a vital air gap that prevents a routine phishing email in the corporate office from becoming a pipeline shutdown. Security teams should also ingest the indicators of compromise (IOCs) provided by CISA into their SIEM and intrusion detection systems, and vigilantly monitor for anomalous traffic patterns, such as unexpected MQTT-over-TLS or DNS-over-HTTPS communications originating from OT segments.
Looking Beyond the Immediate Threat
The activities of CyberAv3ngers and its linked ecosystem are a clarion call for a fundamental reassessment of OT security. As industries rush toward digital transformation and the Industrial Internet of Things (IIoT), the attack surface has expanded dramatically. This incident underscores that security in these environments cannot be an afterthought bolted onto legacy systems designed for isolation. It must be baked into the architecture from the start, with an assumption of constant threat.
The future of critical infrastructure defense will hinge on this integrated approach, blending robust network hygiene, advanced behavioral detection tailored for OT protocols, and a healthy dose of skepticism toward sensational cyber claims. The lesson from this campaign is that our physical and digital realities are now inseparably linked, and defending one requires an unwavering focus on the other.