The Unseen Gateway: How Home Routers Became a Spy’s Dream
Imagine the digital front door to your home office, the humble router blinking quietly in the corner. According to a stark warning from Microsoft Threat Intelligence, that innocuous piece of plastic has become the primary target for a sweeping, state-aligned cyber espionage operation. A group tracked as Forest Blizzard, also widely known as APT28 or Strontium, is systematically compromising thousands of consumer and small-office routers worldwide. Their goal is simple yet devastating: to silently hijack internet traffic and spy on organizations across the globe.
Exploiting the Remote Work Weak Link
Since August 2025, this campaign has successfully breached over 5,000 devices, impacting more than 200 organizations. The attackers are capitalizing on a perfect storm of conditions created by the shift to hybrid work. Many employees rely on consumer-grade routers at home, devices often purchased for their price tag rather than their security pedigree. These routers frequently go unpatched, lack robust monitoring, and sit outside the traditional corporate security perimeter. For a sophisticated actor like APT28, which operates in support of Russian military and intelligence objectives, they are not just vulnerable devices; they are unlocked side doors into sensitive corporate networks.
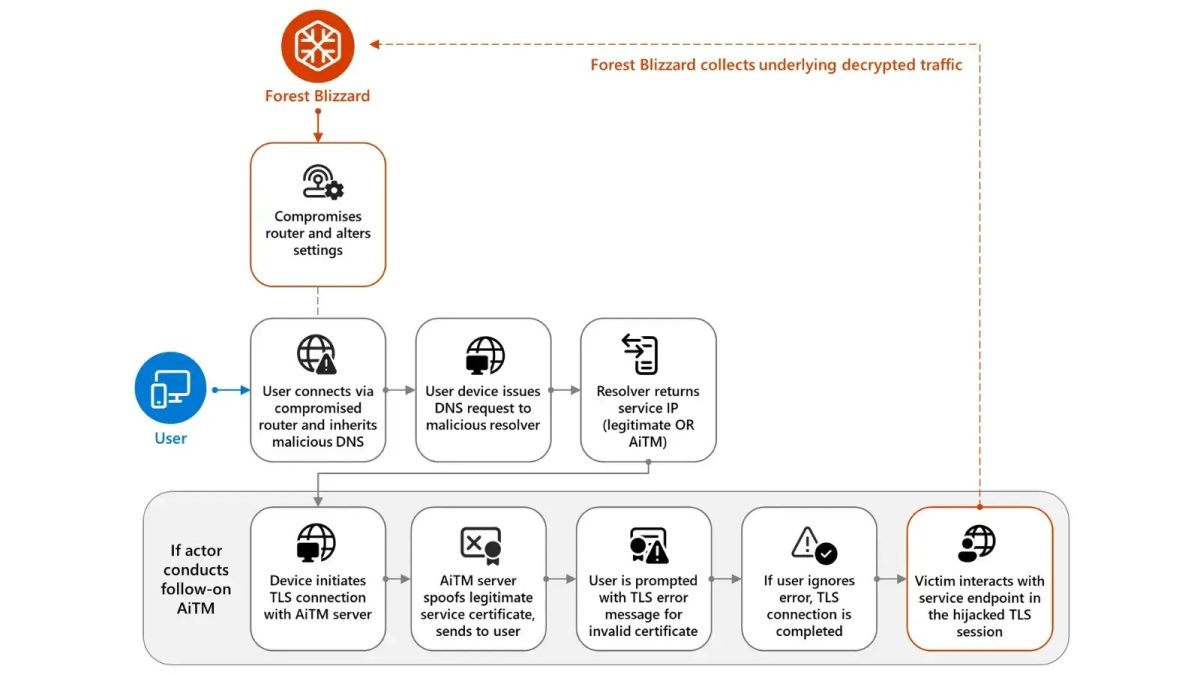
The attack methodology is chillingly efficient. It begins with gaining unauthorized access to these poorly secured routers. Once inside, the hackers perform a subtle but powerful manipulation: they change the device’s Domain Name System (DNS) settings. DNS acts as the internet’s phonebook, translating human-friendly domain names like ‘google.com’ into machine-readable IP addresses. By controlling this directory on the router, the attackers can redirect all traffic from every connected device, be it a laptop, phone, or smart TV, to servers under their command.
The Silent Interception of Everyday Traffic
What makes this so insidious is its transparency to the end user. Your device automatically trusts the DNS server provided by your router. So, when you type in a web address, your request is quietly diverted to a malicious server without a single pop-up or error message. The attackers are even using a legitimate, open-source tool called dnsmasq to manage this redirection, a technique that helps them blend in with normal network activity. By listening on port 53, the standard port for DNS, they can monitor every query, mapping out the digital habits of everyone on the network.
This initial surveillance is just the reconnaissance phase. The real payoff comes with selective, high-value strikes. After identifying targets of interest, often in government, IT, and energy sectors, the hackers launch what’s known as Adversary-in-the-Middle (AiTM) attacks. In these scenarios, a user attempting to log into a trusted service like Microsoft Outlook is seamlessly redirected to a flawless, fake replica hosted by the attackers. Here’s where a critical moment of user psychology comes into play: the fake site will present an invalid security certificate, triggering a browser warning.
How many of us have hastily clicked past such warnings? If the user proceeds, the game is over. The hackers can now intercept everything: usernames, passwords, sensitive emails, and confidential cloud communications. Microsoft has already observed this precise tactic being used against government bodies in Africa. It’s a stark reminder that a moment of impatience can undo layers of corporate security.
From Espionage to Potential Sabotage
The implications extend far beyond data theft. With this level of control, the threat group could escalate operations dramatically. They could deploy malware directly to connected devices, establish a persistent foothold inside corporate networks, or even use the hijacked routers to launch denial-of-service attacks, disrupting critical services. This campaign transforms a mundane piece of consumer hardware into a potent weapon for advanced cyber espionage. It begs the question: when was the last time you updated your router’s firmware?
Building Defenses Beyond the Corporate Firewall
So, what can organizations do when the threat landscape now explicitly includes an employee’s living room? The first step is a fundamental shift in mindset. Home and SOHO routers must be treated as critical enterprise security assets, not an IT afterthought. For remote work setups, companies should strongly discourage the use of consumer-grade equipment and instead provide or subsidize enterprise-grade solutions with proper security management.
Technically, enforcing a Zero Trust DNS policy is crucial. This ensures that corporate devices, regardless of location, are configured to use only approved, trusted DNS servers (like a company’s internal DNS or a secure public service like Cloudflare or Google DNS). This setting overrides any malicious configuration pushed by a compromised router. Furthermore, strengthening identity security becomes the last and most vital line of defense. Organizations must implement phishing-resistant multi-factor authentication (using physical security keys or authenticator apps, not SMS), coupled with conditional access policies that can block login attempts from suspicious locations or networks.
Security teams also need to expand their monitoring. They should watch for anomalous DNS requests from employee devices and ensure detailed logs are maintained to trace any suspicious behavior. While simply resetting a router’s DNS settings can stop an ongoing attack, it’s a reactive measure. If credentials have already been stolen, the damage is already done. The reset button doesn’t undo a breach.
The New Perimeter Is Everywhere
This campaign by Forest Blizzard is more than just another hacking headline. It is a clear signal that the concept of a network perimeter has evaporated. The attack surface now encompasses every device in an employee’s home. For cybersecurity professionals, the challenge is no longer just guarding the castle walls; it’s about securing every potential path to the castle, including the scenic backroads everyone thought were safe.
Moving forward, we can expect state-sponsored groups to continue weaponizing the infrastructure of daily life. The lesson for the next decade of cybersecurity is that resilience will depend on securing identities, encrypting communications end-to-end, and designing systems that assume the local network is already hostile. Because, as thousands of blinking routers now demonstrate, it very well might be.