Stories By Free RDP
-
AI
/ 2 months agoData Activation: The Overlooked Prerequisite for AI Success
The Real Bottleneck for Enterprise AI As we move deeper into 2026, the primary obstacle to successful artificial intelligence deployments is...
-


Vulnerabilities
/ 2 months agoCritical File Upload Flaw in Ninja Forms Plugin Threatens Tens of Thousands of WordPress Sites
A Widespread Threat Emerges in the WordPress Ecosystem A severe security vulnerability has placed over 50,000 WordPress websites directly in the...
-


Vulnerabilities
/ 2 months agoCritical Android Zero-Click Vulnerability Enables Remote Device Crashes
The Silent Threat in Your Pocket Google’s latest Android security update for April 2026 has patched a menacing flaw that security...
-


Vulnerabilities
/ 2 months agoCritical Windmill Platform Vulnerabilities Expose Systems to RCE, PoC Exploit Released
Severe Security Flaws Uncovered in Windmill Automation Platform Cybersecurity researchers have sounded the alarm on a series of critical vulnerabilities within...
-

Vulnerabilities
/ 2 months agoCritical CUPS Flaws Chain to Grant Remote Root Access, Posing Severe Linux Threat
A Perfect Storm in the Print Queue In a discovery that underscores the persistent risks lurking in foundational system software, security...
-

Vulnerabilities
/ 2 months agoAI Uncovers 13-Year-Old Apache ActiveMQ Flaw, Highlighting New Era of Vulnerability Discovery
A Hidden Flaw Surfaces After More Than a Decade The security landscape is witnessing a paradigm shift, not just in the...
-


AI
/ 2 months agoAsylon and Thrive Logic Partner to Deploy Physical AI for Enterprise Perimeter Defense
Beyond Cameras and Alarms: A New Era of Active Perimeter Security The static world of fences, cameras, and motion sensors is...
-


Vulnerabilities
/ 2 months agoThe Silent Listener: How Fiber Optic Cables Can Be Turned into Covert Microphones
A New Frontier in Acoustic Surveillance For decades, fiber optic cables have been the gold standard for secure, high-speed data transmission....
-


Data Breach
/ 2 months agoGPUBreach Attack Unlocks Full System Control, Bypassing Key Hardware Protections
For years, the GPU has been viewed as a powerful but largely isolated workhorse, a specialized processor safely contained within its...
-
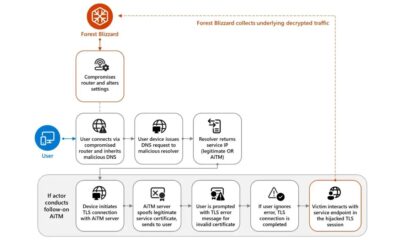

Cyber Attack
/ 2 months agoRussian State Hackers Hijack Home Routers in Global Espionage Campaign
The Unseen Gateway: How Home Routers Became a Spy’s Dream Imagine the digital front door to your home office, the humble...